We often think of cyberattacks as personal problems—a stolen password or a phishing email. But what happens when these threats scale up? A sophisticated community safety cyberattack doesn’t just target one person; it targets the systems we all rely on. Think ransomware shutting down hospitals or digital threats crippling our power grid. The consequences are physical and immediate. It’s why Ready.gov now lists cyberattacks alongside natural disasters, recognizing that these digital threats have very real-world consequences for our safety and critical infrastructure. Understanding these attacks is the first step to building resilience.
Thank you for reading this post, don't forget to install the free PubSafe mobile app and subscribe!
What Is a Cyberattack?
A cyberattack is any malicious attempt to access, damage, or disrupt a computer system, network, or data. According to Ready.gov’s Cyberattack Hazard Information Sheet, cyberattacks can compromise personal financial and health information, disrupt critical infrastructure including hospitals and utilities, spread malware and ransomware across networks, and cause widespread economic damage and service disruption. Nation-states, criminal organizations, hacktivists, and individuals with malicious intent can all launch cyberattacks.
Cybercrime by the Numbers
To understand the scale of the threat, it helps to look at the data. Cybercrime isn’t just a minor nuisance; it’s a massive, organized industry with staggering financial and social consequences. The sheer volume of attacks is hard to comprehend, affecting millions of individuals and organizations. According to the FBI, cyberattacks led to over $16 billion in potential losses from 859,532 complaints filed by the public. These aren’t just abstract figures; they represent real people losing their savings, businesses facing shutdowns, and essential services being put at risk. The numbers paint a clear picture of a widespread problem that requires a proactive approach to security and resilience from everyone.
Financial and Operational Costs
The financial fallout from a single cyber incident can be devastating. In 2024, the average cost of a data breach reached $4.88 million, a figure that includes everything from forensic investigations and system repairs to regulatory fines and brand damage. This cost cripples businesses and strains the budgets of public institutions. Looking ahead, the economic impact is only expected to grow, with some experts projecting that the annual cost of cybercrime will surpass $23 trillion by 2027. These expenses divert critical funds away from innovation, community programs, and disaster preparedness, making it harder for organizations to fulfill their core missions and serve the public effectively.
Who Are Hackers Targeting?
While any individual or organization can become a victim, cybercriminals often focus their efforts on specific sectors where they can cause the most disruption or extract the most value. Industries that handle sensitive data or provide critical services are prime targets. Attackers know that compromising these sectors can have far-reaching consequences, creating chaos and providing leverage for financial gain. Understanding which industries are most at risk helps us anticipate threats and allocate resources to protect our most vulnerable systems, from healthcare networks to the public agencies we rely on during emergencies.
Healthcare and Financial Sectors
The healthcare industry remains the most costly sector for data breaches, with the average incident costing $9.77 million in 2024. An attack on a hospital doesn’t just compromise patient data; it can shut down life-saving equipment and disrupt emergency services, turning a digital threat into a physical one. Similarly, the financial sector is a top target, with 65% of its organizations facing ransomware attacks. When these institutions are attacked, it undermines public trust and can destabilize the economy. The disruption of these critical services highlights the need for robust contingency plans and resilient communication platforms that can operate independently when primary systems fail.
Manufacturing and Government Agencies
Hackers are also increasingly targeting the manufacturing sector and government agencies. Manufacturing was the industry most targeted by ransomware in 2023, with 638 documented attacks that halted production lines and created significant supply chain disruptions. At the same time, federal agencies reported 32,211 security incidents, compromising sensitive government data and interfering with public services. An attack on a government agency can cripple emergency response coordination and communication channels. This is why having a decentralized platform for volunteer coordination and incident reporting is so important, ensuring that communities can still organize and respond even when official systems are down.
Common Cyber Threats to Your Family’s Safety
Recognizing and Avoiding Phishing Scams
Phishing attacks use deceptive emails, texts, or websites to trick users into providing sensitive information. Ready.gov recommends verifying the sender’s identity before clicking any link and using multi-factor authentication on all important accounts.
Ransomware: When Your Data Is Held Hostage
Ransomware encrypts your files and demands payment to restore access. This type of attack has paralyzed hospitals, school districts, and municipal governments. Regular offline backups are the most effective defense.
Data Breaches: Is Your Information at Risk?
Large organizations that store your personal data can be breached, exposing your information. Monitor your accounts and consider identity theft protection services.
What Do Criminals Do with Stolen Data?
Once your information is out there, it can be used in some pretty scary ways. It’s not just about someone knowing your email address. Criminals can use your stolen data to apply for credit cards or loans in your name, drain your bank accounts, or open new utility services. They might even use your identity to get a job or avoid trouble with the police. In many cases, your personal details are bundled up and sold to other criminals on the dark web. According to cybersecurity experts, hackers can use your accounts to spread viruses or trick other people, turning one data breach into a much larger problem for the community. This is why protecting your personal information is a critical part of your overall safety plan.
Spotting Social Engineering Ploys
Attackers may call, email, or approach you in person while pretending to be a trusted entity. Never provide sensitive information in response to unsolicited contact.
How AI Is Changing the Game for Attackers
Just when you think you’ve learned all the tricks, the rulebook changes. Cybercriminals are constantly looking for an edge, and their latest tool is Artificial Intelligence (AI). Hackers, including sophisticated state-sponsored groups, are now using AI to automatically probe for weaknesses in networks, craft more convincing phishing emails, and develop malware that can adapt to avoid detection. This means attacks are becoming faster, more complex, and harder to defend against. While AI also helps cybersecurity professionals, it’s a double-edged sword that has significantly raised the stakes for everyone. Understanding that these advanced tools are in play helps reinforce why basic security hygiene, like strong passwords and being cautious online, is more important than ever.
Spoofing: When Trust Is Used Against You
Spoofing is a tactic where an attacker disguises their communication to look like it’s from a trusted source. Think of it as a digital wolf in sheep’s clothing. This can take many forms, from a fake caller ID that shows a local number to an email that looks exactly like it came from your bank. The goal is always the same: to trick you into giving up sensitive information, clicking a malicious link, or sending money. They might even create a replica of a well-known website that looks identical to the real thing but is designed to steal your login credentials. The key to avoiding spoofing is to always be a little skeptical and verify requests through a separate, trusted channel before taking action.
Hidden Threats: Trojans, Cryptojacking, and Drive-By Downloads
Some of the most dangerous threats are the ones you don’t see coming. A Backdoor Trojan, for example, is a type of malware that creates a secret entry point into your computer, giving an attacker ongoing access without your knowledge. Another sneaky threat is cryptojacking, where malicious code uses your computer’s processing power to mine cryptocurrency for the attacker, slowing down your device and running up your electricity bill. Perhaps most alarming are drive-by downloads, where malicious software can install itself on your device simply by you visiting a compromised website—no clicks required. These hidden attacks show why having up-to-date security software and being careful about the sites you visit is so critical.
Denial-of-Service (DoS): Overwhelming the System
A Denial-of-Service (DoS) attack is less about theft and more about disruption. In this scenario, an attacker floods a server, website, or network with so much traffic that it becomes overwhelmed and crashes, making it inaccessible to legitimate users. Imagine a thousand people all trying to cram through a single doorway at once—nothing gets through. The primary goal is often to cause chaos and financial loss by taking a service offline. For public safety and emergency response organizations, the consequences can be dire. A DoS attack on a hospital’s network or a community’s emergency alert system during a crisis could delay critical care and communication when every second counts.
Stay Ahead: How to Prepare for a Cyberattack
- Keep all software updated. Software updates frequently patch security vulnerabilities. Enable automatic updates for your operating system, browser, and antivirus software.
- Use strong, unique passwords. Use a password manager to generate and store complex passwords. Never reuse passwords across sites.
- Enable multi-factor authentication (MFA). MFA requires a second form of verification beyond a password, significantly reducing unauthorized access risk.
- Back up your data. Follow the 3-2-1 rule: 3 copies of data, on 2 different media types, with 1 copy stored offsite or offline.
- Be skeptical of links and attachments. Verify through another channel before clicking suspicious emails — even if they appear to come from someone you know.
- Secure your home network. Change default router passwords, use WPA3 encryption, and set up a guest network for visitors and smart devices.
Beyond Passwords: Firewalls and Encryption
While strong passwords are your first line of defense, true digital safety requires a layered approach. Think of a firewall as the digital security guard for your network. It stands between your trusted internal network and the untrusted outside world, inspecting all traffic and blocking malicious data before it can cause harm. For public safety organizations, this is non-negotiable. As the Cybersecurity and Infrastructure Security Agency (CISA) notes, cyberattacks can halt emergency services. Beyond the firewall, encryption is crucial for protecting the data itself. Encryption scrambles sensitive information—like incident reports or volunteer details—making it unreadable to anyone without the proper key. This ensures that even if data is intercepted, the personal and operational details within remain secure. Platforms built for disaster response, like PubSafe, use these security measures to protect the sensitive data shared between citizens, volunteers, and agencies during a crisis.
A Cyberattack Is Happening: What Now?
- Disconnect affected devices from the internet and home network immediately
- Do not pay ransom — there is no guarantee attackers will restore your data
- Report the incident to the FBI’s Internet Crime Complaint Center (IC3.gov)
- Contact your bank, credit card companies, and credit bureaus if financial data may have been compromised
- Work with a qualified cybersecurity professional to assess and remediate the damage
How a Cyberattack Can Affect Community Safety
Critical infrastructure cyberattacks are particularly dangerous because they can disable water, power, healthcare, transportation, and communications. The 2021 Colonial Pipeline ransomware attack disrupted fuel supplies across the Eastern U.S. Communities can prepare by maintaining emergency supplies in case utility services are disrupted, signing up for emergency alerts not dependent on internet connectivity, and supporting local government investment in cybersecurity for public utilities.
Targeting the Front Lines: Threats to Public Safety
While individual and corporate cyberattacks are serious, a more sinister trend is the deliberate targeting of public safety infrastructure. These aren’t random attacks; they are calculated efforts to disrupt the very systems we rely on in an emergency. Cybercriminals know that by attacking first responders and their communication networks, they can cause maximum chaos and confusion. According to the Cybersecurity and Infrastructure Security Agency (CISA), public safety communications face specific and growing threats designed to cripple emergency response when communities are at their most vulnerable. Understanding these specific attack vectors is the first step toward building a more resilient defense for our towns and cities.
Telephony Denial of Service (TDoS) Attacks
Imagine hundreds or thousands of automated calls flooding a 911 call center at once, making it impossible for legitimate emergency calls to get through. This is a Telephony Denial of Service (TDoS) attack. Unlike a typical Denial of Service (DoS) attack that targets websites, a TDoS attack focuses on voice communication lines. The goal is to overwhelm the system, create a bottleneck, and prevent dispatchers from answering real calls for help. These attacks can be used for extortion, but they also serve as a dangerous disruption tactic that directly endangers lives by delaying emergency medical, fire, and police responses.
Attacks on Mission-Critical Systems
Cyberattacks are increasingly aimed at the heart of public safety operations. While the total number of attacks on public safety groups has seen a slight decrease, attacks on mission-critical systems have surged by 60%. These systems include computer-aided dispatch (CAD), emergency radio networks, and 911 call centers—the essential tools first responders use to coordinate and react. An attack on a CAD system can wipe out the digital map that shows where police cars are, while an attack on a radio network can silence communication between firefighters at a scene. These targeted strikes are designed to dismantle the technological backbone of an emergency response.
When a 911 Center Goes Down: The Real-World Impact
When a cyberattack successfully disables a 911 center or its supporting systems, the consequences are immediate and severe. It’s not just an IT problem; it’s a public safety crisis that affects people’s lives, health, and security. An attack can disable the computer-aided dispatch system, leaving dispatchers unable to efficiently direct responders to an emergency. It can knock out records management systems, preventing officers from accessing critical background information. In these moments, the speed and effectiveness of an emergency response plummet. First responders are forced to rely on manual methods and outdated paper maps, slowing them down when every second counts.
This is why having redundant and resilient communication channels is no longer a luxury—it’s a necessity. When primary systems are compromised, alternative platforms can fill the gap. A decentralized network allows citizens, volunteer teams, and official agencies to continue sharing information and coordinating efforts. For example, using a mobile app to report an incident with a geotagged location can provide vital data to responders even if the 911 phone lines are jammed. This creates a parallel system of communication that ensures help can still be organized and dispatched, mitigating the chaos caused by a digital attack on central infrastructure.
Why Public Safety Systems Are Vulnerable
Many public safety agencies, especially in smaller municipalities, operate on tight budgets, which can lead to significant cybersecurity vulnerabilities. Attackers often exploit common weaknesses that stem from a lack of resources and specialized IT staff. Problems like poor security configurations, insecure remote access points for employees, and the use of outdated, unsupported software create easy entry points for malicious actors. These vulnerabilities are not just theoretical; they have been directly linked to successful attacks that slowed down how quickly first responders could do their jobs and put entire communities at risk.
Strengthening these systems requires a proactive approach. It involves more than just updating software; it means fostering a culture of security and embracing modern, secure technologies. For agencies looking to enhance their operational resilience, integrating with a broader communication network is a powerful step. When organizations register their teams on a shared platform, they create a more robust and interconnected response ecosystem. This not only provides a fallback during a cyberattack but also improves day-to-day coordination, ensuring that communication lines remain open between public agencies, NGOs, and community volunteers no matter the challenge.
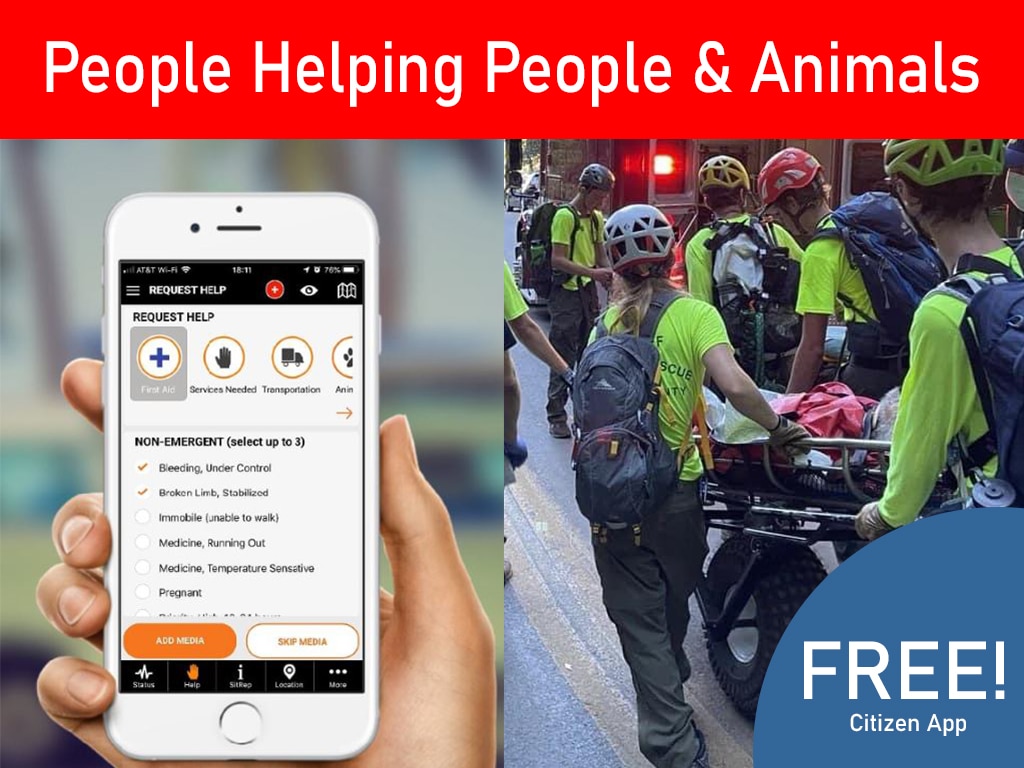
How PubSafe Helps During a Community Cyberattack
One of the most dangerous aspects of a cyberattack on critical infrastructure is that it can disable the communication systems communities use to coordinate emergency response. PubSafe provides an independent, resilient public safety communication layer that functions even when traditional infrastructure is degraded. Users can share status, location, and safety information peer-to-peer, enabling communities to maintain situational awareness even when centralized systems are down. In a world where cyberattacks on infrastructure are increasingly likely, building communication redundancy is prudent emergency preparedness.
Maintaining Operational Continuity When Systems Fail
When a cyberattack hits critical infrastructure, the goal is often to create chaos by knocking out essential services. For emergency responders, the most significant threat is losing communication. If 911 dispatch centers, radio towers, or internet-based coordination tools go dark, it can paralyze an entire response effort. This is where maintaining operational continuity—the ability to keep essential functions running during a crisis—becomes non-negotiable. The core strategy is to build redundancy into your communication plan. This means having backup systems ready that don’t depend on the same vulnerable infrastructure, ensuring a single point of failure won’t leave your community disconnected when it matters most.
A Resilient Platform for Emergency Coordination
A resilient platform provides that crucial backup when primary channels are compromised. Tools like PubSafe create an independent communication layer that functions separately from traditional networks. Because it’s a decentralized, peer-to-peer system, it allows teams and citizens to share real-time information, like their status and location, directly from their mobile devices. This helps everyone maintain situational awareness even when centralized command systems are down. This approach aligns with federal guidance from agencies like the Cybersecurity and Infrastructure Security Agency (CISA), which offers free resources to help public safety groups safeguard their operations. Integrating a resilient platform is a smart, proactive step to ensure your team can always communicate and coordinate.
Your Go-To Cybersecurity Resource List
- Ready.gov Cybersecurity page
- Cybersecurity and Infrastructure Security Agency: cisa.gov
- FBI Internet Crime Complaint Center: ic3.gov
Download the Ready.gov Cyberattack Hazard Information Sheet and take the first steps today to protect your home, family, and organization from digital threats. Connect your community on PubSafe.
Free Federal Resources from CISA
When you’re trying to protect your organization from cyber threats, it can be hard to know where to turn for reliable guidance. Thankfully, the federal government provides a wealth of free resources, and the Cybersecurity and Infrastructure Security Agency (CISA) leads the charge. CISA offers more than just advice; they create practical toolkits and guides tailored specifically for the public safety sector. These aren’t dusty manuals meant to sit on a shelf—they are actionable blueprints designed to help you build a stronger defense and a more resilient response plan. Let’s look at two essential CISA resources that can make a real difference for your team’s preparedness.
Public Safety Communications and Cyber Resiliency Toolkit
If you’re part of a public safety organization, identifying your digital weak spots is the first step toward strengthening them. CISA’s Public Safety Communications and Cyber Resiliency Toolkit is built for this exact purpose. It gives you a clear framework for assessing your current cybersecurity posture and provides best practices to improve the resilience of your communication systems. Because these systems are the lifeline of any emergency response, protecting them is non-negotiable. While the toolkit helps secure your primary infrastructure, a truly comprehensive strategy includes backup communication channels. This is where a platform like PubSafe adds a vital layer of resilience, ensuring your team can maintain emergency coordination even when your main systems are compromised.
The “First 48” Response Guide
The steps you take in the first two days after a cyber incident can determine the outcome. CISA’s “First 48” Response Guide outlines the immediate actions your organization should take to effectively manage a breach. It stresses the need for a pre-established plan to quickly assess the situation, contain the damage, and notify all relevant stakeholders. A critical part of this response is maintaining operational awareness, especially when your standard communication tools are offline. Having a dedicated platform for reporting an incident and coordinating with your team ensures your response doesn’t stall. With a tool like PubSafe, you can keep communication flowing and manage your response without relying on compromised networks.
How to Protect Your Smart Home from Cyber Threats
The explosion of Internet of Things (IoT) devices in American homes — including smart TVs, smart speakers, security cameras, thermostats, doorbells, baby monitors, and connected appliances — has dramatically expanded the attack surface that hackers can target. Many IoT devices ship with weak default passwords, infrequent software updates, and limited security features. They can serve as entry points into your home network, allowing attackers to access other devices, monitor your activities, or launch attacks on third parties.
Ready.gov and CISA recommend these IoT security best practices: Change default passwords on every connected device immediately after purchase. Check for firmware updates regularly and enable automatic updates if available. Segment your network by creating a separate Wi-Fi network (guest network) for IoT devices — this prevents a compromised smart appliance from accessing your computers and smartphones. Research devices before buying — choose manufacturers who provide regular security updates and have a strong security track record. Disable features you do not use, such as remote access if you only use the device at home.
Does Your Business Have a Cyberattack Plan?
For small and medium-sized businesses, cyberattacks pose an existential threat. According to the National Cybersecurity Alliance, 60% of small companies that suffer a cyberattack go out of business within six months. CISA’s Cybersecurity Performance Goals and NIST’s Cybersecurity Framework provide accessible, prioritized guidance specifically for small businesses that may not have dedicated IT security staff.
Key elements of a small business cyber resilience plan include: employee security awareness training (the most cost-effective security investment); multi-factor authentication on all business accounts; a data backup and recovery plan that is tested regularly; an incident response plan that specifies who to call, what to do, and how to communicate if a breach occurs; cyber liability insurance to cover the costs of breach notification, legal liability, and recovery; and a vendor risk management process that ensures third parties with access to your systems meet basic security standards.
The SBA and SCORE both provide free resources and mentorship for small businesses building cyber resilience programs. CISA’s free Cyber Hygiene Services include vulnerability scanning for small businesses and critical infrastructure operators.
Building a “Zero-Trust” Framework
The old way of thinking about security was like a castle with a moat: once you were inside the walls, you were trusted. But what happens when an attacker gets past the gate? A “Zero-Trust” framework flips this idea on its head. It operates on a simple, powerful principle: never trust, always verify. This means every user, device, and application must prove its identity and authorization before accessing any resource, regardless of whether it’s inside or outside the network. To stay ahead, security leaders must understand how attackers operate and implement proactive measures. For platforms that coordinate sensitive disaster response, like PubSafe, this model is essential. It ensures that only verified personnel from different organizations can access critical incident data, maintaining operational security when it matters most.
The 5 C’s: A Framework for Elite Protection
Technology is a powerful tool, but a solid strategy is what makes it effective. The “5 C’s” provide a practical framework for security and response teams: Competence, Confidence, Communication, Coordination, and Control. This approach helps teams assess risks, adapt to changing threats, and manage resources effectively. It’s about ensuring your team has the skills (Competence), believes in the mission (Confidence), shares information clearly (Communication), works together seamlessly (Coordination), and maintains command of the situation (Control). Effective coordination, for example, is where a shared platform becomes invaluable, creating a common operating picture that allows different agencies and volunteer groups to work as one cohesive unit during a crisis.
The Human Element: Key Skills for Security Teams
Ultimately, your greatest security asset isn’t a piece of software; it’s your people. The most advanced tools are only as effective as the teams who use them. Elite security and response personnel rely on a specific set of personal skills to succeed under pressure. These include clear communication, constant watchfulness, and the ability to remain calm in chaos. Courage and compassion are just as critical, driving team members to act decisively while remembering the human impact of their work. These are the people who make a difference on the ground, whether they’re managing a complex cyber incident or using a tool like the PubSafe app to report a hazard and help their neighbors. Technology empowers these skills, but it can never replace them.
The Bigger Picture: National Cybersecurity Efforts
Ready.gov’s inclusion of cyberattacks in its national hazard preparedness framework reflects a broader recognition in the federal government that cybersecurity is a national security issue with direct public safety implications. CISA’s role as the nation’s cyber defense agency has expanded significantly, with new authorities to coordinate vulnerability disclosure, share threat intelligence with the private sector, and respond to major incidents. The Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) now requires operators of critical infrastructure to report significant cyber incidents to CISA within specified timeframes, improving the federal government’s situational awareness and response capabilities.
At the individual and community level, building a culture of cybersecurity awareness is as important as any technical measure. Connect your community on PubSafe and use it as a trusted channel for sharing verified information about local cyber incidents that may affect community safety — such as a cyberattack on a local utility, hospital, or government system.
Putting Your Cybersecurity Plan into Action
Preparedness is not a single action — it is an ongoing practice. Every time you review your emergency plan, check your supply kit, or connect a neighbor to a preparedness resource, you are building community resilience. The cumulative effect of thousands of individuals and families taking preparedness seriously is a community that absorbs shocks, recovers faster, and takes care of its most vulnerable members during the worst days.
Bookmark the relevant Ready.gov hazard page, download the Hazard Information Sheet, and share this article with your family, coworkers, and neighbors. Join the PubSafe network to stay connected with your community before, during, and after any emergency. Check your local emergency management agency’s website for preparedness resources specific to your region. And consider volunteering with local emergency response teams — CERT (Community Emergency Response Team), volunteer fire departments, and local emergency management councils all welcome community members who want to contribute to a more resilient community.
Emergency preparedness does not require perfection. Start where you are, with what you have. Each small step builds on the last, and the journey from being unprepared to being genuinely ready is shorter than most people think. Take one step today — for yourself, for your family, and for your community.
Frequently Asked Questions
I’m not in public safety. How does a cyberattack on critical infrastructure actually affect me? That’s a great question because it gets to the heart of the issue. A major cyberattack isn’t just an IT problem for a power company or a hospital; it has a direct ripple effect on your life. Imagine your power going out, your tap water stopping, or local government services becoming unavailable. An attack on a hospital could delay emergency care for you or a loved one. An attack on a supply chain could mean empty shelves at the grocery store. These digital threats have very real, physical consequences that can disrupt the basic services we all depend on.
Our organization is small and on a tight budget. Where should we even start with cybersecurity? It can feel overwhelming, but you don’t need a massive budget to make a significant impact. The most effective first step is focusing on your people. Regular security awareness training helps your team become the first line of defense against threats like phishing. After that, enable multi-factor authentication (MFA) on all your accounts. It’s a simple, powerful way to block unauthorized access. Finally, take advantage of the free resources from federal agencies like CISA, which offers toolkits and guides specifically designed for organizations with limited resources.
If a cyberattack takes down official communication channels, what’s the alternative? This is exactly why having a backup plan is so important. When primary systems like 911 or official alert networks are compromised, communication can’t just stop. The alternative is a resilient, decentralized network that doesn’t rely on that same central infrastructure. Platforms like PubSafe allow citizens, volunteer groups, and agencies to communicate directly with one another using their mobile devices. This creates a parallel system for sharing information, reporting incidents, and coordinating help, ensuring the community can still organize even when official channels are silent.
What’s the difference between protecting my personal data and protecting my smart home devices? Think of it like this: protecting your personal data (like passwords and financial info) is like locking your filing cabinet. You’re preventing thieves from stealing your identity and assets. Protecting your smart home devices (like cameras, speakers, or thermostats) is like locking the doors and windows to your house. If a hacker gets into a poorly secured smart device, they can gain a foothold on your entire home network, potentially spying on you or using your network to launch other attacks. Both are critical, but they protect you from different kinds of intrusions.
The article mentions a “Zero-Trust” framework. What does that mean for a regular person or a small team? Zero-Trust sounds technical, but the idea is simple: never trust, always verify. In the past, security was like having a guard at the front gate; once you were inside, you were trusted everywhere. A Zero-Trust approach is like having a guard at every single door inside the building who asks for your ID each time. For you or your team, it means adopting a mindset where you always verify requests for information, even if they seem to come from a trusted colleague. It also means using tools like multi-factor authentication that constantly prove you are who you say you are before granting access.
Key Takeaways
- Cyberattacks Have Real-World Consequences: These digital threats are not just about stolen data; they can shut down hospitals, disrupt 911 services, and cripple utilities, turning a virtual problem into a physical crisis for your community.
- Basic Security Habits Are Your Best Defense: You can protect yourself and your family by adopting simple, powerful practices. Use a password manager for unique passwords, enable multi-factor authentication on all important accounts, and always verify requests for personal information.
- Plan for Communication Failure: During a major cyber incident, primary communication systems like 911 or official networks can go offline. A resilient response plan must include a backup communication tool that allows teams and community members to share information and coordinate efforts independently.